The increasing level of fraud in various areas of life, especially in banking, leads to the development of new types of customer identification. Behavioral biometrics is one of these. Despite its wide usage, for many people, it still sounds like something out of Science Fiction. In this article, you will find out what behavioural biometrics is, how exactly it works and learn the sophisticated differences between it and physical biometrics.
What is Behavioral Biometrics
In simple terms, it is a system of measurement and analysis of human-specific behavioral traits based on human-computer interaction. It involves the collection of a wide variety of data that is unique to the user, such as the speed of pressing certain keyboard keys, the user’s manner of using a mouse, or the way of holding a smartphone and swiping the screen.
The combination of these cues in different mathematical algorithms allows obtaining a more complete and precise user profile that, in its turn, lets detecting fraudsters fairly early (even before they act).
Although behavioral biometrics are also known as dynamic biometrics, they are also called passive because end-users don’t have to take any extra actions to be verified. It doesn’t require to say anything into a microphone or put fingers on any particular button. Users need just behave as usual.
Behavioral biometrics solutions can be subdivided into various types that are used either separately or in certain combinations by identity verification service providers all over the world.
Here are some of the most common:
Keystroke Dynamics
Also often called as typing biometrics, It is an algorithm that analyses and defines a user’s typing pattern. It consists of detailed timing information describing when precisely each key is pressed and when it is released when one is operating a keyboard
Signature Recognition
It is a type of behavioral biometrics that identifies/authenticates a person based on their handwriting. It incorporates analysis of the direction and pressure of the pen (or in other cases the user’s finger) stroke along with the overall shape of the signature for the user identity verification.
Gesture Recognition
This identification/authentication technique uses machine-learning algorithms to perceive and interpret user’s motions as the primary source of data input. The software then compares real-time gestures with ones saved in the library to verify genuine users and reject any fraudulent imposters.
Voice Recognition
Voice or speaker recognition is the method based on receiving and interpreting the unique patterns in the user’s voice to confirm the identity of the speaker. It is often confused with speech recognition, which is the practice of recognising what a person says.
Gait Recognition
This behavioral biometrics method analyses the way of a person’s walking style and pace, determined by the unique combination of individual characteristics that include age, body shape, height and weight of the person. This method allows to quickly identify any human from afar.
Lip Motion
This type of biometrics identifies users according to their visual lip movements while speaking. The software records the activity of the muscles around the mouth to build up and store a specific pattern. Later it allows or denies access to the data/site/account depending on the correlation analysis of the real-time recording with the one previously saved.
Advantages and disadvantages of behavioral biometrics
As it might be clearly seen, behavioral recognition systems are largely driven by artificial intelligence and machine learning techniques. These technological advancements vastly change the perception of human identification and cybersecurity. AI picks up human patterns throughout their usage of the devices and applications while software passively runs in the background. A big advantage of using a biometric access system is its very high accuracy. It aggregates hundreds of human-computer interaction signals to generate a sort of bionic cyber identity for every authentic user. These unique characteristic patterns of behavior are very difficult to steal or duplicate which makes it a great response to ever-increasing regulatory requirements. In addition, it provides a magnificent hassle-free customer journey. Instead of entering countless passwords and codes, which the majority of people find exhausting, behavioural biometrics provides a passive verification of users without them being necessitated to make any effort. And yet, experts debate the pros and cons.
Let’s take a closer look:
Pros:
- A unique combination of analysed behavioral characteristics for each real person
- Smooth integration methods, no need for custom script change to carry out identity verification
- Improves verification accuracy in multimodal identification systems
Cons:
- As behavioral biometrics are not widely validated, implementation of it can be costly
- Requires lots of personal data to figure out and build up a user’s typical behaviour
- Not always can be accurate in unimodal identification systems since human behaviour is not always regular. People may behave differently when they are in a hurry, tired, drunk or feel unwell
Physical Biometrics
If behavioral biometrics works with the unique ways in which a real person acts, physical (physiological) biometrics counts on the measurements of the human body for identity verification/authentication. This includes face geometry, fingerprints, certain parts of the eye, vein patterns, and other corporal traits. To put it simply, physical biometrics replace “things that you know” (passwords and PINs) with “things that you are”. This type of biometrics uses a hybrid method of analysis, that combines human expertise and the power of artificial intelligence, which altogether gives quite high accuracy results. Static physical biometrics represent the most popular nowadays technique for genuine user identification. They are used by the majority of the companies (almost 80% worldwide) which collect and store physical biometric data to authenticate identities for all sorts of uses.
Let’s have a closer look at the most popular physical biometrics methods:
DNA Matching
This method is based on the unique sequences of the human’s genetic material. A prepared for control DNA sample (blood, saliva, or other body secretions and tissues) is used to create a DNA profile, which is later compared with another sample to determine their identity.
Ear Acoustic Authentication
Special headphones with the microphone measure reflecting inaudible sound waves inside the ear. A created digital model of the ear shape is used as a biometric template for later matching with the ear shape of the genuine person.
Eye Vein Recognition
This type of biometric verification uses the vein patterns of the eyeball (the white of the eyes), which are unique to every human. The process consists of capturing the image and its segmentation, extracting particular features and matching them with ones in the database.
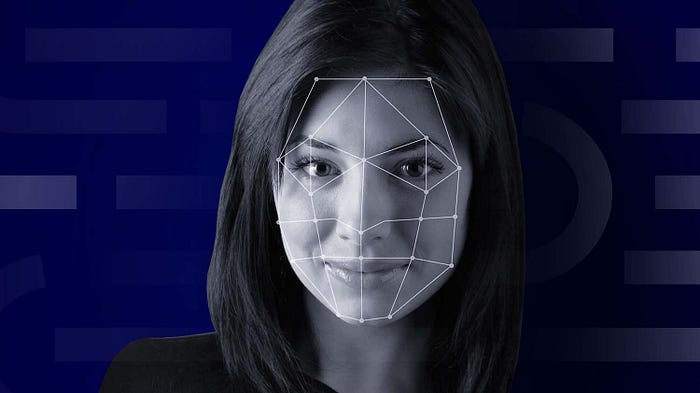
Facial Recognition
This is one of the most popular biometrics techniques due to its non-intrusive nature and simplicity. A 3D image of the face is built using facial attributes (the eyes, eyebrows, nose, lips), their location and shape as well as the distance between them.
Finger Vein Recognition
This type of identification uses the same principle as eye vein recognition. Near-infrared light Illuminates the veins in the fingers; software collects the sample, saves the pattern and uses it later to match it to the template.
Fingerprint Recognition
This is the oldest method of biometric recognition known to humanity. Basically, it is the analysis of the ridges and valleys formed on fingertips, which are unique for each person including identical twins.
Footprint and Foot Dynamics
The structure of the grown human foot stays the same throughout a person’s life without any significant changes which make this method almost as accurate as fingerprints. It is based on the calculation of such parameters as foot length, height, weight, and even BMI.
Hand Geometry
This method is a bit outdated and is not so often used nowadays. It is based on the measurement of the overall structure, proportions and shape of the hand (width, length and thickness of joints and fingers), and certain characteristics of the skin surface area such as ridges and creases.
Iris Recognition
This method uses iris images captured in the near-infrared bandwidth which are converted into a digital code afterwards. The iris colour is not relevant, only the structure is used for the recognition process. This makes it possible to work even with black and white images.
Body Odor Recognition
It is the newest method of biometric verification. The approach is based on analysing skin secretions (or simply, sweat) to build an amino acid profile that is unique to every individual. Unfortunately, there are still certain technological challenges to solve before this method can be used in practice.
Palm Print Recognition
This approach uses the recognition of certain characteristics on the palms of the hands which are scanned and recognised by a special way configured camera or another device.
Palm Vein Recognition
This method is an advanced form of vein recognition. B&W CCD camera with near-infrared LED array pass through the skin surface to read the veins beneath it. The image is captured, digitised and used to confirm identity.
Retinal Scan
The retina is a thin layer of tissue at the back of the human’s eye. Every retina is unique because of the complex structure of capillaries that supply blood to it. Though retinal scan is widely used, it is considered to be not a user-friendly technique.
Skin Reflection
The method (also known as skin spectroscopy) is based on the interaction between radiation and human skin. It is done by exposure of a skin area to the light of different wavelengths which is later analysed for each wavelength.
Thermography Recognition
This is a process of identification using a thermal camera that captures an image of an individuals’ thermal patterns by using infrared radiation emitted from them. Same as fingerprints, thermograms are unique even among identical twins.
Advantages and disadvantages of physical biometrics
Biometrics aims to create a registration system that never denies access to authorized users and, at the same time, keeps the non-legit intruders at the bay. Compared to “old-school” methods of verification such as passwords and codes, physical biometrics delivers a way more reliable protection: after all, our bodies can’t be lost or stolen. Modern technological development allows using advanced scanners to read human characteristics such as fingerprints and retinas. For example, retina scanner has become the most common type of standard biometrics today. And yet, its static nature of physical traits has certain downsides too. If the templates of an individual’s physical features are revealed once, they can be used multiple times by bad actors.
Pros:
- Identifying physical traits are indivisible from the individual; they cannot be forgotten or lost
- It is relatively hard to fake identifying physical traits
- The procedure of verification is quick and mostly AI-driven
Cons:
- Some types of physical biometric identification require certain environmental conditions
- In some cases biometric identifiers can be damaged, thus become impossible to read
- Certain physiological biometric scanners are way too expensive to implement widely
- A high level of personal biometric data protection is required to comply with regulatory obligations

What Type of Biometrics Is the Most Accurate?
According to the statistics of FRR (False Rejection Rate) and FAR (False Acceptance Rate), iris recognition is considered to be the most accurate type of biometrics. The iris’s unique folds and muscle characteristics together with advances in scanning technologies allow verifying the identity of the individuals with outstanding accuracy.
The only problem with it (and with the other physical biometrics in general) is the dependency on the eagerness of the users to share this highly sensitive personal data without firm guarantees on whether it will be stored well and if it will be shared with the third parties. Yet, today this issue is strictly regulated worldwide, and the only concern of the companies is choosing the reliable AML compliance software vendor.
What Is the Safest Type of Biometric?
Behavioral traits are nearly impossible to replicate by another person and, therefore, they can be called the safest type of biometrics. Being non-contact en masse, this statement is especially true in the modern context of the Covid pandemic.
And yet, today, the industrial implementation of behavioral biometrics is not widespread. At best it is used in cases where additional verification levels are required — for example, when conducting large transactions or providing access to highly sensitive data.
Thus, behavioral biometrics are most often used by banks and financial institutions. Although, there is a huge potential for their implementation in e-commerce, online services, healthcare, government, and consumer electronics.
Final Thoughts
It seems that behavioral biometrics can create a more trustworthy identification process than its precursor physical biometrics. Cutting-edge advances in Artificial Intelligence and machine learning have pushed humanity on a path towards a more intelligence-driven identification procedure, which verifies legitimate users simply by analysing their behavior while they interact with their devices.
This approach also means that users don’t need to share sensitive personal data, which in its turn protects both the users and the companies from the risks posed by data breaches.
Yet, despite these advantages, physical biometrics are still critical to the future of identification because of their unique nature.
So, instead of counting on a one-size-fits-all solution, businesses need to consider a multi-layer-based approach that will combine the distinctive identification methods offered by both physiological and behavior biometrics. This is the only way to create a fast, safe, and user-friendly online experience, along with confronting people’s concerns and potential security flaws. One of the companies that offers a solution on this is ZignSec.
